
DATA-CENTRIC SECURITY
Introduction
The emergence of strict new data privacy regulations, such as GDPR and CCPA, is driving the need for CISOs to more effectively address data protection and data governance in complex and geographically-diverse hybrid IT ecosystems. The terms pseudonymization and anonymization are now common in the context of these privacy regulations when it comes to data protection and privacy. While pseudonymization of data still allows for some form of re-identification (even indirect and remote), while anonymization of data cannot be re-identified. CISOs look to the vendor community for data security solutions to address these privacy requirements but struggle with the confusing array of security models and services. Enterprises must choose a solution that offers a variety of data protection formats that not only allow pseudonymization and anonymization of sensitive data, but also enable business processes, analytics workloads, etc. to operate on the data in its protected state. Format-Preserving Encryption is a powerful data protection technology, and is currently becoming the de facto standard across the industry. FPE warrants a deeper examination, and the following section expands on FPE and its importance.
Format Preserving Encryption
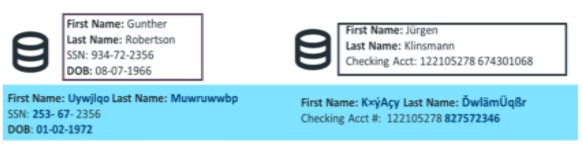
Format-Preserving Encryption (FPE) refers to encrypting data in such a way that the output (the ciphertext) is in the same format as the input (the plaintext). “Format-preserving” implies that encrypting a 16-digit credit card number produces a ciphertext which is another 16-digit number; encrypting an English word produces a ciphertext comprising the same number of English characters; and so forth.
These properties have several benefits and simplify data protection, especially for legacy applications, where it avoids major redesign and refactoring of applications and business processes:
- Minimal or zero database schema impact – FPE facilitates retrofitting encryption technology to existing devices or software where conventional encryption modes would not be feasible. In particular, database applications may not support changes to data length or format.
- Minimal or zero data storage impact – Since length preservation is an inherent property of FPE, enterprises do not have to worry about additional storage usage, unlike conventional (non-format-preserving) encryption methods, which typically expand data. Note: Some exceptions do apply where the length of the output with some variants of FPE can be slightly longer than that of the input data.
- Analytics on protected data – Format-preserved protected data elements such as credit card numbers, SSNs, etc., can still be used as index keys to facilitate statistical research, even across databases. With FPE, the same inputs to the algorithm will create the same ciphertext. This deterministic encryption preserves the referential integrity of the data and thereby the ability to glean valuable information from the protected dataset. Other crucial benefits of Secure Analytics enabled by the use of FPE is expanding the access to data across a broader set of analysts, and potential monetization of data sets, without compromising on security and privacy.
- Cross-application dataflow preservation – FPE lets protected data flow across applications without requiring changes to those applications to accept the protected data, an infeasible approach with conventional encryption methods, since applications require data of specific lengths and formats.
- Using protected data without requiring decryption – FPE can allow protection of only specified key portions of data elements, enabling use of the data in its protected state. For example, the “first six” digits of credit card numbers are used for charge routing, and the “last four” of SSNs is used for customer verification. If these are left in the clear, many applications in the data flow will not need access to the entire data element, and can perform required business functions without requiring any change to the applications, and not requiring to perform any decryption. Such partial encryption can facilitate functions such as sort and certain search use cases, such as “Starts with”, “Ends with”, etc., without requiring any decryption of the encrypted data.
- Test data management – FPE can also be used to obfuscate/scrub production data to populate test databases, enabling realistic test conditions based on production volume, variability, etc.
NIST Special Publication 800-38G, Recommendation for Block Cipher Modes of Operation: Methods for Format-Preserving Encryption, specifies two AES modes, FF1 and FF3, for format-preserving encryption. However, NIST has concluded that FF3 is no longer suitable as a general-purpose FPE method based on findings of cryptanalytic attacks on the FF3 algorithm. Few vendors have implemented FPE within their data security solutions. Customers need to be cautious about other vendor implementations of FPE, ensuring that they are not using the vulnerable FF3 mode or a non-standard form of FPE not validated by NIST.
Note: FPE on Unicode - Normalization is normal in Unicode processing, and is a critical issue for format-preserving data protection, because if a protected value contains any normalizable characters, any normalization after encryption will destroy the ciphertext. Most solutions offering format-preserving data protection for Unicode generally try to avoid the issue by simply saying “Never normalize ciphertext”. Since one of the benefits of format preservation is the ability to pass data through other applications in its protected state, and normalization may occur at many points in the life of a data element, this is not a good solution. Ensure you pick a solution which can solve the Unicode normalization problem by providing Safe Unicode FPE. Safe Unicode FPE provides a robust and elegant solution to the normalization problem, allowing Format-Preserving Encryption of Unicode data without risk.
