CLOUD DATA SECURITY
Introduction
Enterprises across industry segments are moving IT workloads and functions to the cloud, frequently ahead of any strategy or consistent capability to secure sensitive data. The advantages of cloud migration, such as scale, agility, and consumption-based pricing, are compelling and seem to outweigh the risks in the short term. Most enterprise IT today is hybrid, with some workloads in the cloud and some hosted within the enterprise datacenter. Many are adopting a “cloud-first” or “cloud-only” approach for all new IT functions and business. Due to a combination of decentralized IT functions, frequent mergers and acquisitions, and shadow IT, most enterprises are multi-cloud, leveraging more than one cloud service provider (CSP). Data security is rarely the first consideration for the selection of a CSP. The emergence of strict new data privacy regulations, such as GDPR and CCPA, is driving the need for CISOs to more effectively address data protection and data governance in complex and geographically-diverse hybrid IT ecosystems. The terms pseudonymization and anonymization are now common in the context of these privacy regulations when it comes to data protection and privacy. While pseudonymization of data still allows for some form of re-identification (even indirect and remote), while anonymization of data cannot be re-identified. CISOs look to the CSPs for data security solutions to address these privacy requirements but struggle with the confusing array of security models and services they offer. CSPs offer native key management, encryption, and Hardware Security Module (HSM) services. These security services have typically been added as a layer on top of their existing stacks; after-thoughts from a late recognition of their customers’ increasing data security concerns, and are not enterprise-grade. As most enterprises are also multi-cloud, the challenges inherent in CSP security offerings include deficiencies in uniformity, homogeneity, coverage, customer control and ownership, functionality, scalability, performance, visibility, and more. On top of these, there are broader challenges with key management, and vendor lock-in. In this article, we describe the various data-centric security offerings of the “Big Three” CSPs—Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure. We make an attempt to objectively reflect on what their data security services entail, based on the published documentation made publicly available by the CSPs. It also outlines what enterprises should be aware of prior to consuming these services in the context of their belated yet increasing capabilities in the data-centric security space. It also needs to be noted that the information captured is a point-in-time assessment and is subject to change as the CSPs continue to enhance and expand their services. This article is intended towards any and all audience who deal with data security and cloud security, executives, hands-on IT and Security professionals, and anyone with a passion or interest in cybersecurity in general, across enterprises and service providers.
Cloud Service Provider Crypto and Key Management Services
As enterprises transition from being just compliant to being secure, they must focus on data-centric security services that keep their sensitive data protected persistently—while at rest, in transit, and in use—rather than server-side or transparent encryption services across storage and databases, which offer very little actual security. The good news is that even the CSPs have realized the increasing need for data-centric security, and have started to offer new capabilities in this space. CSPs offer two kinds of cloud cryptographic (crypto) services to enable the implementation of data-centric security:
- key broker and key management services (KMS), such as AWS KMS, GCP KMS, and Azure KeyVault; and
- cloud hardware security modules (HSMs), such as AWS CloudHSM.
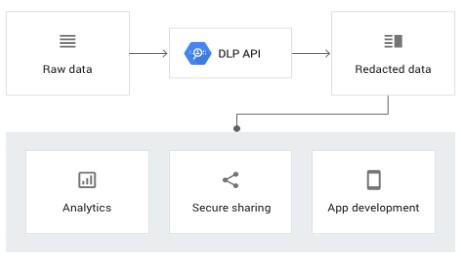
This whitepaper also touches upon the Google Cloud DLP service, which is a composite service that detects sensitive data and applies policies on the detected data.
CSP Key Management Services
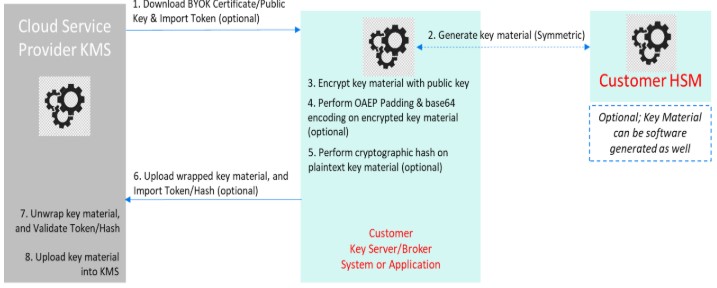
Key broker and key management services typically expose an API for managing keys and secrets. The premise of key management or brokerage across all of the big three CSPs is the use of the Master Key and Working Key model. The Master Key, usually referred to as the Customer Master Key (CMK), never leaves the KMS application, and is not used to protect sensitive data in bulk. It is typically used to generate Working Keys and/or to encrypt Working Keys or other secrets, and thus serves as a Key Encryption Key (KEK). Working Keys are Data Encryption Keys (DEKs), and are used by applications to encrypt/decrypt actual sensitive data. AWS and GCP use symmetric (AES-256) CMKs, but Azure uses only asymmetric (RSA-2048, -3072, -4096) key pairs, storing the private keys in their KMS.CMKs may either be software-managed or stored inside a FIPS-compliant HSM controlled by the CSP. There are different models of Master Key management in terms of customer control and visibility:
- Customer-managed Master Key: Customer can view key metadata and manage the key
- CSP-managed Master Key: Customer can view key metadata but cannot manage the key
- CSP-owned Master Key: Customer cannot view key metadata nor manage the key
Cloud HSM
Cloud HSM is a service through which keys are generated by, and stored within, FIPS 140-2-compliant HSMs that are hosted and managed by the CSP. This model allows higher throughput than the KMS-based model of encryption. These HSMs offer a subset of the PKCS#11 standard API specifications, which are exposed either directly or through the KMS interface to take advantage of the other cloud services integrations existing with the KMS.An important caveat is that these CSP crypto services are available in specific physical locations, referred to Regions. Even when these services are available, cross-region integrations and availability of keys across CSP regions are also not guaranteed. Some CSPs do not specify their level of FIPS 140-2 compliance.
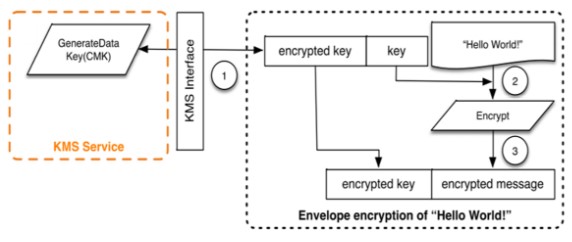
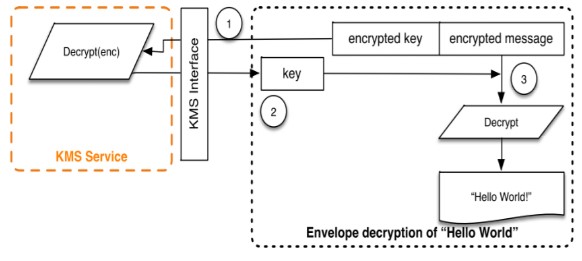
Envelope Encryption
While these KMSs are used to generate, store, protect, and retrieve encryption keys, it is important to understand the mechanism of application-level data encryption implemented and supported at these CSPs. CSPs implement envelope encryption, which is the practice of encrypting plaintext data with a working key (a DEK), and then encrypting the DEK with a master key (the CMK). CSPs typically offer software development kits (SDKs) that are used by the application to perform envelope encryption.
The encryption process works like this:
- An application makes a request (using the SDK) to the KMS to generate a DEK, under a specific pre-provisioned CMK. Note: With certain CSPs, KMS requests go through the internet by default.
- Across the 3 CSPs, the process for generation of the DEK varies. For AWS, the KMS uses the CMK to generate and encrypt a DEK when an application calls a specific method (GenerateDataKey) in KMS. Each key request results in the creation of a unique DEK that is created and protected under the same or multiple CMKs. However, in the cases of Azure and GCP, the DEK is generated locally but is protected by the KEK that is stored in their respective KMS services. Note: One best practice that is common across these services is the use of unique DEKs for each data during a write operation, and hence negating the need for DEK rotation.
- In case of AWS, the KMS returns both the plaintext and encrypted versions of the DEK to the application. However, there are options such as obtaining just the encrypted DEK by specifying a separate method (GenerateDataKeyWithoutPlaintext).
- The application uses the plaintext DEK to encrypt the sensitive data, and then typically deletes the plaintext DEK from memory.
- The encrypted DEK and the encrypted data are stored together. Note: For CSPs that offer only asymmetric key pairs for DEK encryption, the application/SDK uses the public key of the pair to encrypt the DEK during storage.